Urlsnark is used to sniff HTTP requests from live network traffic and even offline .pcap files. This tool can help us determine which websites were visited by the clients on a network. For this exercise, we are going to use the conference.pcap file from https://www.honeynet.org/node/1220.
To get started, download and the save offline on your device. Use the urlsnarf –p <file> command to get all the HTTP data:
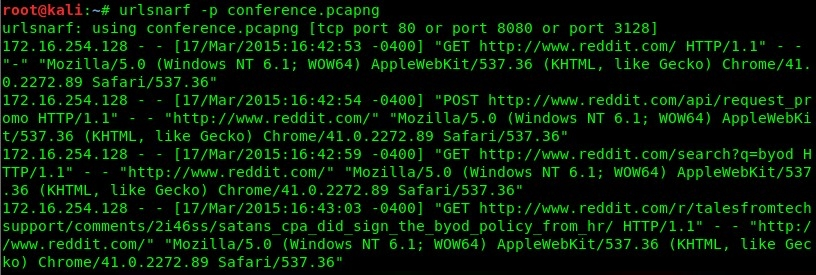
However, as you can see, the output is very overwhelming. Let's create a filter to provide us only with the HTTP URLs from this file. We can use the following command:
urlsnarf -p conference.pcapng | grep "http://" | cut -d "/" ...

