CHAPTER 8Protecting the Inner Perimeter
In general, after you get past the outer perimeter defenses, you can think of the inner perimeter as part of the three-level structure illustrated in Figure 8.1. Consider this perimeter as consisting of the operating system and its application programs that form the gateway to the data stored in the interior zone (folders and files).
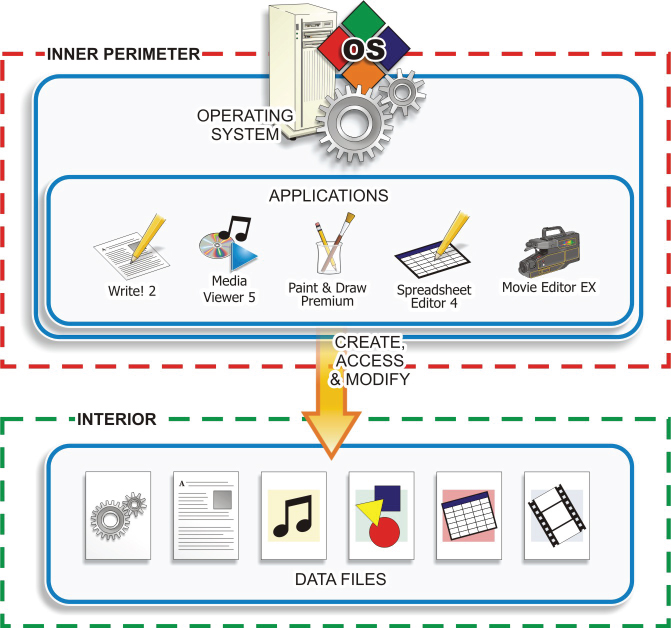
FIGURE 8.1 The Inner Perimeter
- Describe Local Login and User Configuration Options for Host Devices.
- Compare and Contrast the Security Features of Common Operating Systems.
- Identify Common Logging and Auditing Options for Windows and Linux Based Systems
- Explain Options ...
Get Cybersecurity Essentials now with the O’Reilly learning platform.
O’Reilly members experience books, live events, courses curated by job role, and more from O’Reilly and nearly 200 top publishers.

